Base DN: dc=myserver,dc=mydomain,dc=com
Bind DN: uid=root,cn=users,dc=myserver,dc=mydomain,dc=com
The password configured is password for the ‘root’ user
Configuration for Cisco ASA / AnyConnect
aaa-server SYNOLOGY protocol ldap aaa-server SYNOLOGY (Inside) host 192.168.1.100 ldap-base-dn dc=myserver,dc=mydomain,dc=com ldap-scope subtree ldap-naming-attribute uid ldap-login-password <root user password> ldap-login-dn uid=root,cn=users,dc=myserver,dc=mydomain,dc=com server-type auto-detect
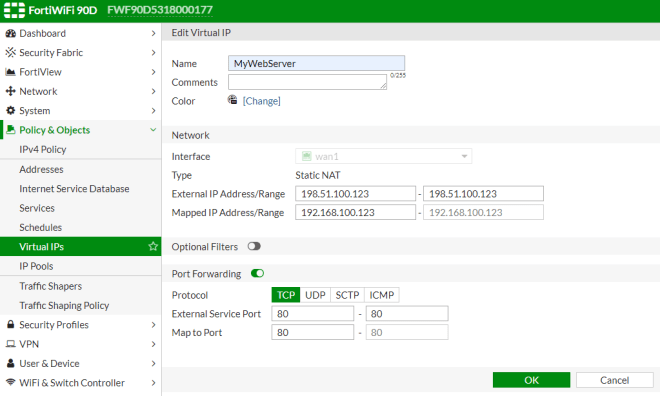
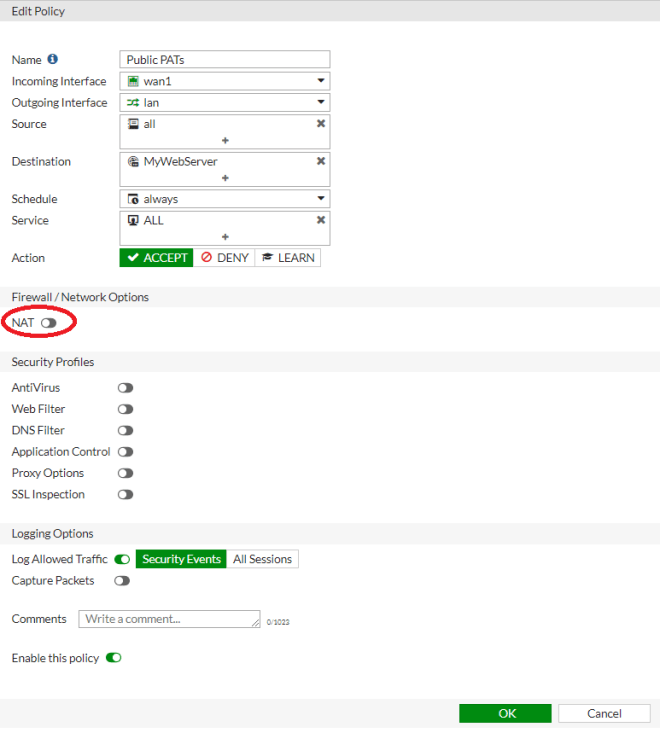
Configuration for FortiGate GUI
- Common Name Identifier = uid
- Distinguished Name = cn=users,dc=myserver,dc=mydomain,dc=com
- Bind Type = Simple
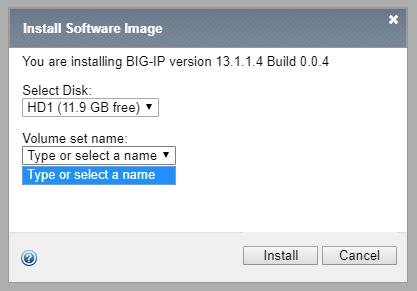
Configuration for F5 BigIP
Need to change Authentication from ‘Basic’ to ‘Advanced’ to set Login LDAP attribute
- Remote Directory Tree: dc=myserver,dc=mydomain,dc=com
- Scope: Sub
- BIND DN: uid=root,cn=users,dc=myserver,dc=mydomain,dc=com
- Password: <root user password>
- User Template: uid=%s,cn=users,dc=myserver,dc=mydomain,dc=com
- Login LDAP Attribute: uid
To use Remote Role Groups:
Attribute String: memberOf=cn=users,cn=groups,dc=myserver,dc=mydomain,dc=com