Came across this while rolling about Palo Alto GlobalProtect. The knowledge base article suggests installing the cert in the browser’s store, which isn’t really helpful in understanding what the cause or solution was in my case.
There’s also its cousin, which complains about a missing client certificate when connecting to the Gateway:
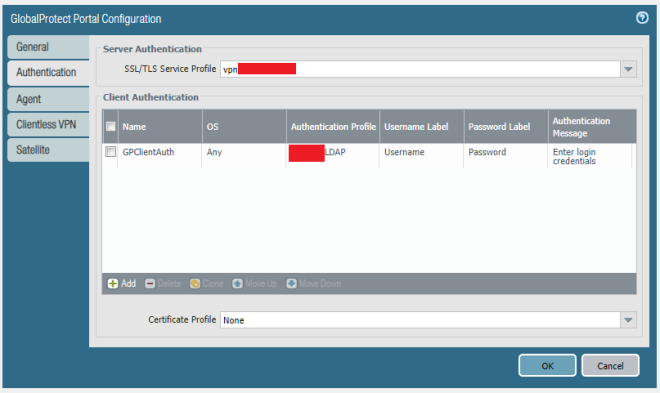
The problem lies in the Certificate profile configuration. I had understood this to be a way to chain intermediate certs; in fact, that happens automatically when the certificate is upload. Rather, this setting controls the CA for client side certs. If if you’re not using client side certs, the configuration should simply have Certificate Profile left to “None”
This is really help me!!!
Thank You.
LikeLike