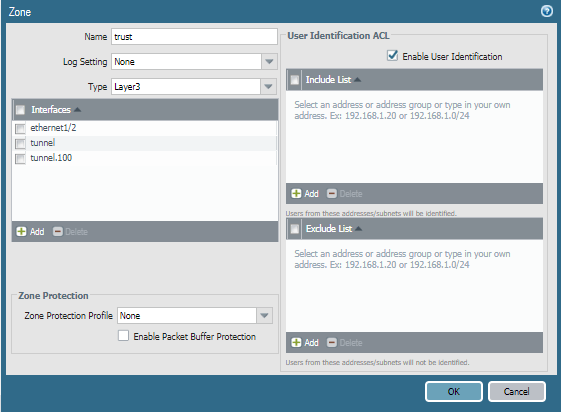
I wanted to write a firewall rule to allow only Active Directory group(s) to access a given zone, destination IP, or service. Since the users would be connected directly to the Palo Alto via GlobalProtect, user tracking was already happening. The clients are in source zone “Trust” and user identification was already checked.
I followed the steps in this KB article to configure group mapping but found two major gotchas. In the Authentication Profile, the user domain must be entered. After doing this, users began showing up as domain\username rather than just username. Secondly, in the group mapping configuration, user domain needed to be blank.
I can now write a rule with mydomain\group as the source user.
Common gotchas
In the source zone, make sure the User-ID option is checked.
In Device -> Server Profiles -> LDAP, set the base DN to something at a higher level than all the groups, and set the Bind DN to an account with privileges to lookup group membership.

In Device -> Authentication Profile, set User Domain to the abbreviated AD domain

Under Device -> User Identification -> Group Mapping Settings tab, leave the User Domain field blank.

Useful troubleshooting commands
Check user to IP address mapping table
show user ip-user-mapping all
Get list of LDAP groups
show user group-mapping state all
Check group membership for a certain LDAP group
show user group name mydomain\myGroup